User:AdaptL/Monero
- Add a blurb about privacy doctrine and technique
Monero is a cryptocurrency notorious for implementing a number of improvements over BitCoin that were first outlined in a protocol called CryptoNote[1]. Notably, it uses a combination of ring signatures and zero-knowledge proofs called "RingCT" to obfuscate the sender, receiver and amount of a transaction[2].
These privacy features prevent the use of BitCoin's SPV (Simplified-Payment-Verification), so it's necessary to distribute the software in two separate programs: The Wallet (Client) software has control over funds and is minimum needed to make a private transaction and accept payments. The wallet connects to a Node (Server) that may run on the same computer or on another computer over the network. The Node connects to the peer-to-peer network, stores and relays transactions, and works together with with other computers on the network to come to consensus about the order in which they occur.
Cryptocurrencies like BitCoin use Proof-of-Work to make it difficult for an attacker to reverse the order of transactions (which would allow the attacker to spend funds more than once). Unlike BitCoin, Monero uses a Proof-of-Work system which is designed to mitigate the effectiveness of specialized hardware (ASICs) as opposed to general-purpose CPUs[3]. Because of this, it becomes necessary to distribute Mining Software for everyday users that may wish to secure the network with their own hardware. This article discusses methods for mitigating cryptojacking attacks.
Most packages listed here are still on the GURU overlay. See this page for information on how to use GURU
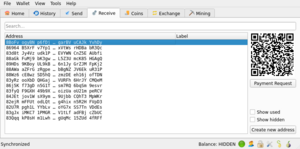
Wallet
Feather Wallet
Currently still on GURU
Feather Wallet is a lightweight and simple Qt5/Qt6 implementation of the monero wallet.
root #emerge --ask net-p2p/featherBy default it's configured to connect to a remote node over the internet (and to onion sites if the tor daemon is running).
To connect feather wallet to a local node instead, select File>Settings>Network>Node>Add custom node(s) and add 127.0.0.1:18081 to the custom nodes list.
monero-wallet-cli
Currently still on GURU
The command-line wallet is packaged with net-p2p/monero:
root #emerge --ask net-p2p/moneroIt can be summoned with:
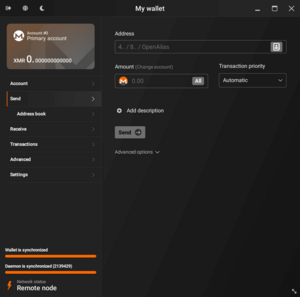
user $monero-wallet-cliMonero GUI
Not packaged yet, you can try compiling from source or using .AppImage
The official Monero GUI is not currently packaged in gentoo, but is still available as an executable .AppImage file from getmonero.org. It is rather bloated and includes monerod, monero-wallet-cli, and P2Pool within the same executable, which may be convenient for some.
Node
monerod
Currently still on GURU
monerod is the only "official" node implementation.
Installation
root #emerge --ask net-p2p/moneroConfiguration
Because the monero blockchain can take up quite a lot of space (about 107 GB as of 2023[4]) The two most important configuration settings are the directory in which it is stored (/var/lib/monero by default), and whether or not it should be "pruned". Pruning is an option that reduces storage usage by about 60%, storing an incomplete but usable copy of the blockchain[5]. Below is an example configuration file at /etc/monero/monerod.conf that changes both of these options:
/etc/monero/monerod.confSetting blockchain directory and pruningdata-dir=/your/monero/directory/
log-file=/your/monero/directory/monero.log
prune-blockchain=1
See monerod options and monerod.conf for a more complete list of configuration options
Service
To start immediately:
root #rc-service monerod startTo start the monerod service on system boot, add it to the default runlevel:
root #rc-update add monerod defaultTo get monerod's current status:
user $monerod statusMining Software
To incentivize users to secure the network with Proof-of-Work, 0.6 XMR is randomly rewarded to every 2 minutes to a successful miner[6]. You can calculate your average expected return by multiplying the your expected hashrate, dividing by the total network hashrate, then subtracting the total cost of electricity consumed. See the monero mining calculator. Generally speaking, monero mining is not profitable unless you have access to relatively modern CPUs and cheap electricity, or you are using your computer for indoor heating. GPU mining is also possible with monero, but it is far less profitable compared to other cryptocurrencies.
While monerod does support mining by itself, it's recommended to use a faster mining implementation instead of monerod's built-in mining.
XMRig
XMRig is the largest fast implementation of Monero mining. This gentoo package respects the opencl USE flag for AMD GPUs, however the use of Nvidia GPUs through CUDA requires a separate plugin.
Installation
USE flags for net-misc/xmrig RandomX, CryptoNight, KawPow, AstroBWT, and Argon2 CPU/GPU miner
root #emerge --ask net-misc/xmrigUsage
If you have a monero node running on the same computer (localhost on port 18081), solo mining is as simple as
user $xmrig -u YOUR_MONERO_ADDRESS Another option is pool mining, which eliminates the need to run a monero node, and may offer more regular payouts at the cost of increased centralization and fees. Configuration depends on the pool, but usually looks something like:
user $xmrig -o your-mining-pool.com:port -u YOUR_MONERO_ADDRESS Optimization
Disabling "hardware prefetchers" has been shown to increase mining performance by about 30%. This can be done by using the wrmsr command as shown in /usr/bin/randomx_boost.sh. XMRig automatically runs this script when you run XMRig as root.
Enabling "1GB huge pages" also yields a slight performance improvement on linux systems, at the cost of using more memory. This is done through the /usr/bin/enable_1gb_pages.sh script.
See also the RandomX Optimization Guide
P2Pool
Currently still on GURU
P2Pool is a decentralized method of spreading out mining rewards into regular payouts, similar to a regular mining pool but with lower fees. The P2Pool software connects to a monero node and exposes a pool that miners such as XMRig can connect to.
Installation
root #emerge --ask net-p2p/p2poolUsage
p2pool can be started in the current directory by running
user $p2pool --host MONERO_NODE_ADDRESS --wallet YOUR_PRIMARY_ADDRESSWhere MONERO_NODE_ADDRESS is the address of the monero node (for example, 127.0.0.1 for a monero node that runs on the same computer), and YOUR_PRIMARY_ADDRESS is a monero primary address (begins with a "4" as opposed to a secondary address that begins with an "8") that will receive the mining reward. Once the P2Pool software finishes connecting to the network, you can start mining with XMRig as if it's a normal pool. By default, this is exposed on port 3333:
user $xmrig -o 127.0.0.1:3333There are currently two different networks: p2pool and p2pool-mini. If your computer has a lower hashrate, you may want to connect to the p2pool-mini network instead by passing the --mini flag to p2pool:
user $p2pool --mini --host MONERO_NODE_ADDRESS --wallet YOUR_PRIMARY_ADDRESSSee also P2Pool FAQ
Troubleshooting
monerod can't sync
Sometimes monerod can get stuck if the computer is forcibly shutdown (for example, electrical outage or running out of battery). This can usually be fixed with monerod --db-salvage.
Cryptojacking Prevention
Cryptojacking is the act of hijacking a computer to mine cryptocurrency against the owner's will. Because of the CPU-bound nature of Monero's Proof-of-Work system (RandomX), it's easier for a hacker to capitalize on a victim's computing power relative to the rest of the network. However, RandomX also has some features designed to mitigate cryptojacking.
It is often speculated that a large portion of monero's hashrate is a result of cryptojacked "IoT" devices (appliances such as cameras, toasters, etc. that contain computers which are unnecessarily connected to the internet). It is important to consider RandomX's Memory-hardness on low-end devices, which prevents it from running at all on computers with less than 256 MiB of memory, and massively decreases mining efficiency on devices with less than 2080 MiB.
Cryptojacking can often be used to extract additional money from a hacked VPS service at great cost to the client. One feature of RandomX is that efficient miners will necessarily leave a detectable trace in the state of CPU registers. "RandomX Sniffer" is a proof-of-concept tool that can be used to detect cryptojacking malware. In theory, VPS providers could use this method to warn clients or prevent cryptojacking though the use of Virtual Machine Introspection. If the client has a firewall installed, then they can also just monitor outbound connections to common monero pools.
Lastly, a common another attack vector is web mining (sometimes referred to as "Drive-by Mining"), which involves the insertion of mining scripts into webpages, taking advantage of the computers that access the web page. Web miners are particularly inefficient because of the decrease in branch prediction speeds and the lack of directed rounding support for floating point operations in JavaScript and WebAssembly. As such, web mining is typically orders of magnitude less efficient than mining natively. If you host a web service, you should pay special attention to securing your website against cross-site scripting attacks. As a user there is not much that can be done to avoid web mining besides installing an ad-blocker or disabling javascript altogether. Some browsers like Firefox have default settings to block common crypto mining scripts. It's also important to consider Web extensions as another vector for web mining.
Privacy Considerations
TODO: research this a bit more.
Intro
TODO:
- Mixnets
- Anonset
- Sybil
Cryptocurrency evangelists (of Monero, Bitcoin, Zcash, etc.) tend to make exaggerated claims about privacy which carry grave consequences for their respective users. It is important for users understand how obfuscation methods work in Monero and other cryptocurrencies and how users can be de-obfuscated.
Degree of Anonymity or "Anonymity Set" with respect to mixnets (Tor, CJ, etc.).
Monero's weak point is its use of ring signatures to obfuscate senders. Because of this, it is susceptible (Enemy-Victim-Enemy) "Poisoned output" attacks[7]. Multisig, Churning, Atomic swaps (not sybil proof). So-called "Dust attacks" are one variant of this.
Networking (Not nessisarily Public)
- Correlation attacks
- Tor, I2P, others?
- Number of relays
- sybil resistance
- vulnerabilities and attack surface, browser fingerprints
- dandelion++
Obfuscation systems (Nesisarily Public)
Quantum-Proofing? Create a Table? Defacto anonyminity set vs Maximum Anoniminity set
- Monero (Ring signatures, CT)
- Zcash (ZK-SNARKs)
- Bitcoin
- CoinJoin, Payjoin
- CoinSwap
- Payment channels, Privacy decreases with respect to routing ability. Consequences of fungibilty on L1
- Firo/Zcoin (???)
- Litecoin (MimbleWimble)
- Chaumian Cash (Blind signatures)
Heuristics
- decoy count
- decoy selection
- scripting (including features like RBF, briefly mention RBF vs 0-conf)
- scriptless scripts
- timing hueristic
- (Enemy-Victim-Enemy) "Poisoned output" attacks[7]
- Multi-output transactions
- Account-based vs UXTO and Hierarchical-Deterministic (HD) wallet
- UXTO Privacy not nessisarially broken until payment (although perhaps SPV changes this)
Threat model/Conclusion
Clearnet vendors vs Clearnet buyer vs DNM vendor vs DNM buyer.
Long term privacy (time until vuln) vs short term fungibility.
Warrant Canaries, other common stuff.
Mention that View-only wallets are broken until seraphis
Libraries
Monero Ecosystem Contains some libraries for linking monero code to external C++, Java, Python, and Node.js Javascript projects. It also includes some example projects and learning materials.
Monero-rs is a similar monero library for the Rust programming language.
MoneroPy is a demonstration of some programming concepts in monero. See also MiniNero and the Zero to Monero tutorial.
References
- ↑ https://web.archive.org/web/20201028121818/https://cryptonote.org/whitepaper.pdf
- ↑ https://web.getmonero.org/library/Zero-to-Monero-2-0-0.pdf
- ↑ https://github.com/tevador/RandomX/blob/master/doc/design.md
- ↑ https://localmonero.co/blocks/stats/blockchain-growth
- ↑ https://www.getmonero.org/resources/moneropedia/pruning.html
- ↑ https://localmonero.co/knowledge/monero-tail-emission
- ↑ Jump up to: 7.0 7.1 https://www.youtube.com/watch?v=iABIcsDJKyM